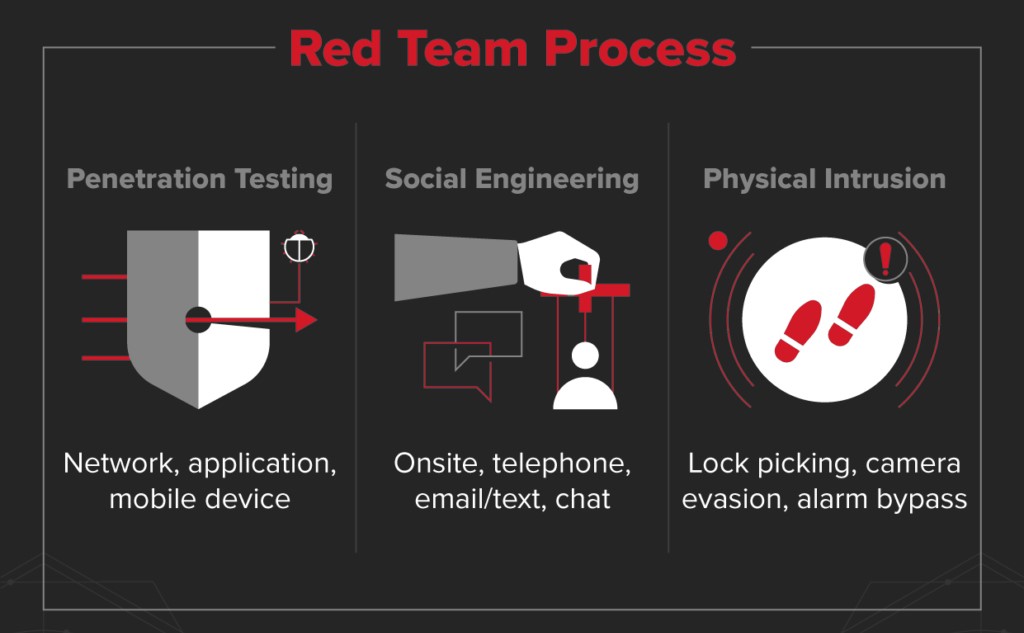
A Red Team can be an externally contracted group of pen testers or a team within the organization, but in all cases, their role is the same: to emulate a genuinely malicious actor and try to break into the system and the infrastructure.
The value of Red Teams can be understood most easily by imagining a fictional scenario. An organization might have an extremely well-developed pen-testing process and therefore be confident that its systems can’t be breached by external actors
A worryingly high number of organizations do not have the control they think they do over their data, for instance, that on average 22% of a company’s folders are accessible to every employee, and that 87% of companies have over 1000 sensitive, stale files in their systems.
Once you’ve completed several business cycles of vulnerability and pen testing, you can start Red Teaming. At this point, the real value of Red Teaming can be realized. However, attempting to bring in red teaming before getting a good handle on the basics will produce very little value.

the role of the pen tester is quite tightly delineated. The work of pen testers is organized into four broad phases: planning, information discovery, attack, and reporting. As you can see, pen testers do more than just looking for software vulnerabilities. They’re thinking like hackers: after they get into your system, their real work begins.
They’ll continue to do more discovery and then base new attacks on what they learn as they navigate through folder hierarchies. And that’s what makes pen testers different from someone hired just to find vulnerabilities by using, say, port scanning or virus sniffing software. An experienced penetration tester can identify:
-
Where a hacker might target you
-
How they would attack
-
How your defenses would fare
-
The possible magnitude of the breach
Reconnaissance
In the reconnaissance stage, we select a target of attack. we obtain most of the information about the target company needed for an attack, such as the email account for spear phishing and the internal personnel system of the company, through search engines and social media. Additionally, the attacker creates a phishing page and collects employees’ email account information, Internally Domain Enumeration, Domain user’s enumeration, List computers in the domain, etc..
Resource development
In this stage, we construct the infrastructure to be used in attack. we secure infrastructure that has not been exposed before for purposes of information leakage and command control. We compromise the server of a small company or rents hosting or domain through virtual assets, and directly creates the malware needed for anattack. However, we also prepare open hacking tools or vulnerability POC codes for flexible attacks depending on the situation. To successfully control a company from the inside, we will use an account intercepted through spear phishing to look through email exchanges or check company or employee information in real time by acquiring a reliable social media account
Initial access
Once we obtain the necessary information, infrastructure, and resources, we will attempt initial access. Initial Access consists of techniques that use various entry vectors to gain their initial foothold within a network. Techniques used to gain a foothold include targeted spear phishing and exploiting weaknesses on public-facing web servers. Footholds gained through initial access may allow for continued access, like valid accounts and use of external remote services, or may be limited-use due to changing passwords.
Execution
Execution consists of techniques that result in adversary-controlled code running on a local or remote system. Techniques that run malicious code are often paired with techniques from all other tactics to achieve broader goals, like exploring a network or stealing data. For example, we might use a remote access tool to run a PowerShell script that does Remote System Discover Most of these techniques do not require a Tool but just access and Native Tools from the Windows Machine itself one of the reasons we want to use Execution on Windows-Signed binaries is to mainly avoid detection
Persistence
Persistence consists of techniques that we use to keep access to systems across restarts, changed credentials, and other interruptions that could cut off their access. Techniques used for persistence include any access, action, or configuration changes that let them maintain their foothold on systems, such as replacing or hijacking legitimate code or adding startup code. Many tools are great for these Post-Exploitation techniques such as Empire, Cobalt Strike, Covenant, Kodiac, Merlin, Metasploit and many other's we can also just use a simple ncat shell that acts as a listener, we can also use RDP sessions where in our post-exploitation we create and add a user to this, to access the target machine.
Privilege Escalation
Privilege Escalation consists of techniques that we use to gain higher-level permissions on a system or network. we can often enter and explore a network with unprivileged access but require elevated permissions to follow through on their objectives. Common approaches are to take advantage of system weaknesses, misconfigurations, and vulnerabilities. Examples of elevated access include:
• SYSTEM/root level
• local administrator
• user account with admin-like access
• user accounts with access to specific system or perform specific function
These techniques often overlap with Persistence techniques, as OS features that let us persist can execute in an elevated context.
Defense Evasion
Defense Evasion consists of techniques that we use to avoid detection throughout their compromise. Techniques used for defense evasion include uninstalling/disabling security software or obfuscating/encrypting data and scripts. we also leverage and abuse trusted processes to hide and masquerade our malware. Other tactics’ techniques are cross listed here when those techniques include the added benefit of subverting defenses.
