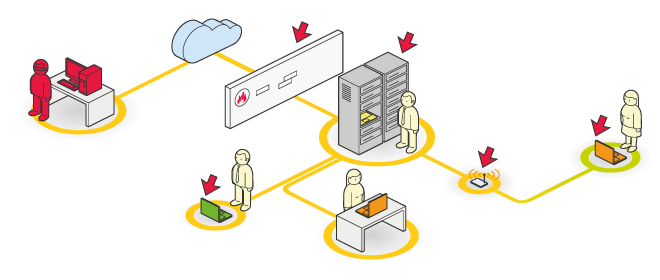
A securely configured IT asset, including systems, network devices, applications, and security solutions, is a crucial component of any defense strategy against criminal activity.
Your critical IT infrastructure equipment's security setup is carefully checked by iSec Security Configuration Review.
Verifying an asset's operational status and the efficacy of its security configuration is the goal of the evaluation.
A more thorough and full explanation of the configuration details for each network and security device, system, and security solution will be provided in the review.
iSec adheres to the CIS and PCI DSS security standards, as well as the best practices of each vendor.
The majority of commonly used systems should go through configuration checks,
- Network Devices
- Firewalls
- IPS/IDS
- Operating Systems
- Internal Systems
- Identity Service Management
- Wireless Networks
