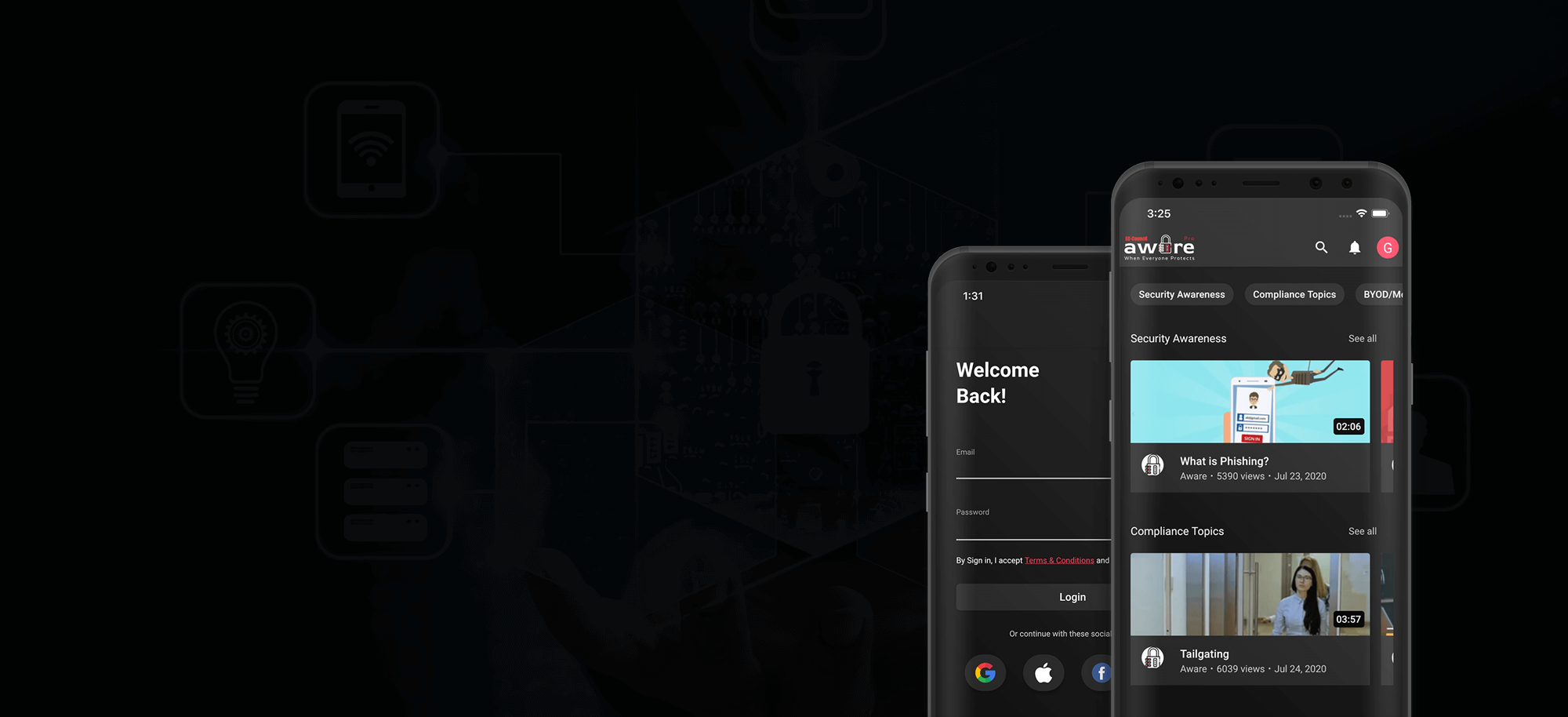
Security awareness training prepares members of an organization, including employees, contractors, temporary workers, and everyone else that completes authorized functions online for an organization, with the necessary information to defend themselves and secure their organization’s assets from damage or loss.
-
Automatic enrollment
-
Customizable e-learning content
-
Customizable Training certificates
-
Scheduled reminders
-
Upload your training content
-
Advanced & automated reporting


Aware gives organizations access to a plethora of videos, interactive cyber security awareness content, and pre-designed modules to select from. These trainings are:
- Interactive and ensure that learners enjoy the learning experience.
- Customizable to allow you to select a theme with relevant topics for your industry and business culture.
- Developed in-house by experienced designers leveraging best practices for maximum effectiveness in changing behavior.